-
Connect With Your Ottawa IT Service Company at (613) 828-1384
Connect With Your Ottawa IT Service Company at (613) 828-1384
In cybersecurity, insider threats pose a significant risk to organizations. These threats often come from individuals within the organization who misuse their access to sensitive information. Understanding the digital indicators of an insider threat is crucial for protecting data and maintaining security.
In this article, you’ll explore three key digital signs that may indicate an insider threat. By identifying these signs early, you can proactively prevent data breaches and safeguard your company’s assets.
One clear sign of an insider threat is when an employee downloads an unusually large amount of data. Regular tasks usually don’t require massive downloads, so it’s a red flag when someone suddenly starts downloading files in bulk.
You might notice spikes in data transfer that aren’t easy to explain. This could involve confidential documents, customer information, or proprietary software. Monitoring such activity helps you catch potential threats early.
Employees accessing sensitive data outside of their normal job functions should receive special attention. This behavior is unexpected and warrants further investigation. A pattern of large downloads often precedes data breaches.
You can use monitoring software to track file transfer activity. Such tools alert you to abnormal data access and download behaviors. Ensuring employees only access the data they need will also help limit insider threats.
Downloading large amounts of data often happens just before someone leaves a company. This is especially true if they resign suddenly or are about to be terminated. Keeping an eye on these patterns can help you act quickly.
Employees might be tempted to take information with them for future use at another job or for malicious purposes. You can intervene before any damage is done by spotting these large downloads.
Always look for unusual download times. If an employee is downloading large files late at night or outside of business hours, it’s concerning. This indicates they might be trying to avoid detection.
It is crucial to have strict policies regarding data downloads. Clear guidelines and regular audits to ensure compliance will strengthen your defenses against insider threats.
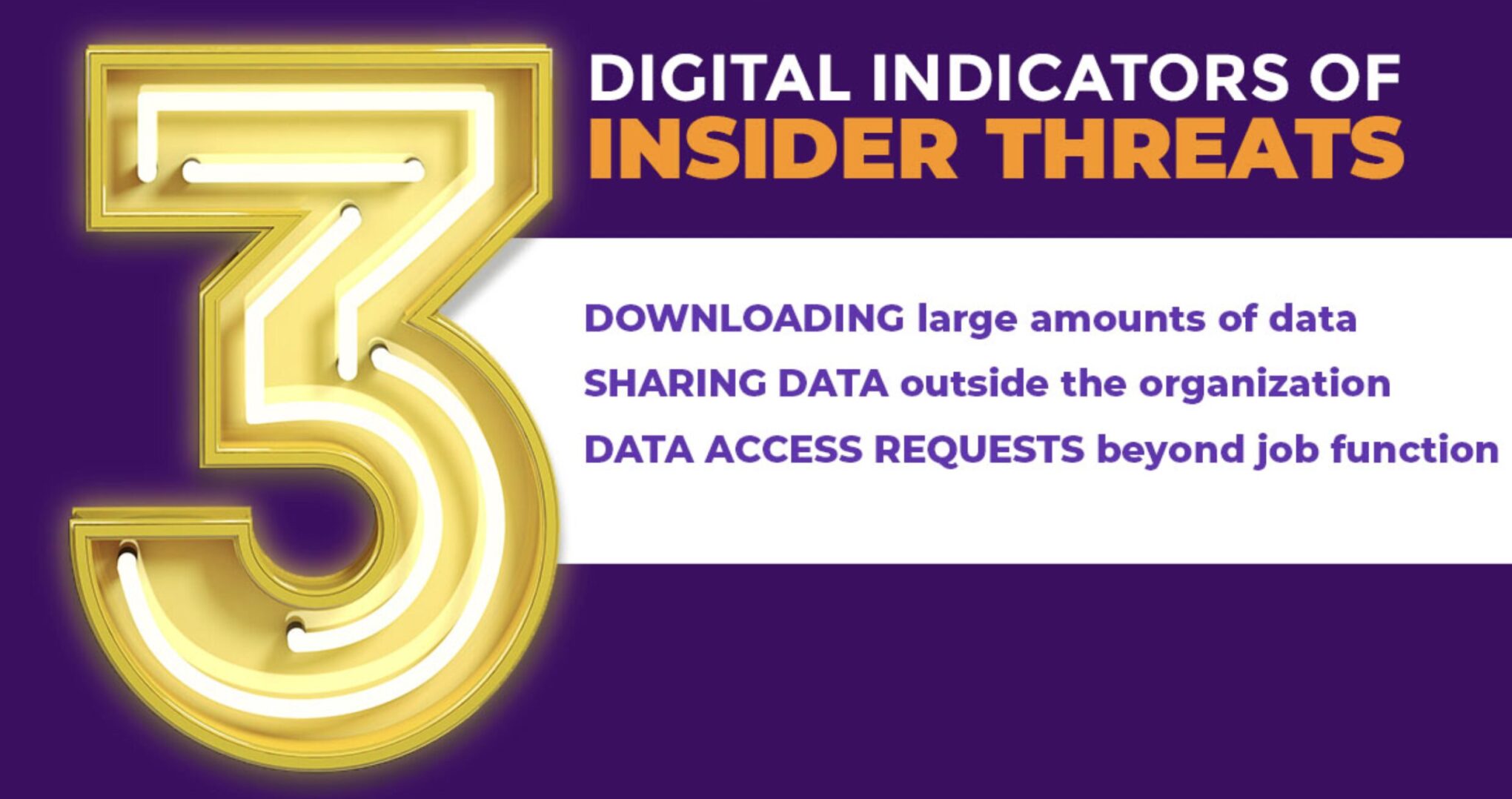
Sharing data outside the organization can be a major indication of an insider threat. If an employee sends sensitive information to personal email addresses or external accounts, it raises a red flag.
Observe the patterns and frequency of data transfers. Regular, unauthorized data transfers might indicate an insider is exfiltrating information for malicious purposes.
Check if employees are using unauthorized tools or networks. Sharing data using personal cloud storage services or social media can put your organization’s security at risk.
Monitor the communication channels employees use. If secure channels are bypassed for less secure ones, it could signal an intention to leak information.
Keep an eye on file-sharing behavior. Large file transfers to unknown or external recipients should be scrutinized. This behavior might be part of a data exfiltration plan.
Watch for employees accessing data outside their job scope. If an employee handles data irrelevant to their role and shares it outside, it’s a warning sign.
Track data access during unusual hours. If data is shared outside normal working hours, especially if it’s unauthorized, it could indicate malicious activity.
Pay attention to sudden shifts in behavior. An employee who starts sharing data externally without clear reasons may need to be investigated.
Consider the use of automated tools. Sometimes, insiders use scripts or programs to automate data transfers, which can be harder to detect manually.
Always enforce strict data-sharing policies. Clear guidelines on what is acceptable and regular audits can help in the early detection of insider threats sharing data externally.
One key indicator of an insider threat is when someone requests access to data that does not align with their job role. This is a red flag because employees should only access information necessary for their job duties.
For example, if a marketing employee asks to view detailed financial records or engineering documents, this could indicate an issue. This behavior suggests they might be seeking information for malicious purposes.
It is important to monitor and track access requests within your organization. Look out for any unusual patterns or repeated attempts to access restricted data.
You can also set up systems to automatically flag such requests. This will help you identify potential threats early and take necessary action before any damage is done.
Another way to manage this risk is by regularly updating access permissions. Ensure that employees can only access information relevant to their current role. This minimizes the chances of unauthorized access requests.
Train your staff to recognize and report suspicious activities. Encourage a culture of security awareness to help prevent insider threats. With everyone alert and informed, potential threats will be harder to ignore.
These steps help safeguard your organization’s sensitive information, ensuring it remains secure from internal threats.
Insider threats come from within the organization, often by employees or associates with access to sensitive information. Recognizing the types of inside threats and their consequences is crucial to protecting your organization.
The consequences of inside threats can be severe. Financial Loss is a direct result of fraud or data theft. Organizations might spend a lot on recovering from breaches and compensating affected parties.
Each type of inside threat requires specific measures to detect and mitigate potential risks effectively.
Recognizing digital indicators of insider threats is vital for securing your organization’s resources. Key indicators include unusual network activity, anomalous data access patterns, and behavioral red flags.
One sign of an insider threat is unexplained network activity. Insider threats might access systems during odd hours or use more bandwidth than typical users. Employees working late on sensitive data or frequently using VPNs without a clear reason should be flagged.
Network monitoring tools can help. Implement these tools to track login times, IP addresses, and data transfers. Look for repeated login attempts, unknown devices accessing your network, or excessive data being moved internally. Regularly reviewing these logs will help you identify threats early and respond swiftly.
Insider threats often manifest through unusual data access. You should watch for users accessing data outside their job role or making repetitive requests for sensitive information. For example, a marketer looking at HR records or a salesperson viewing engineering plans is a red flag.
To manage this, role-based access controls are crucial. These controls ensure that employees only have access to the information necessary for their job functions. Additionally, set up alerts for access to sensitive files and consider using data access governance tools to detect and report abnormal behavior.
Digital behavior changes can also signal an insider threat. Notice if an employee suddenly shows disinterest in work, displays signs of distress, or drastically changes their work patterns. These behaviors may accompany unusual digital activities, such as excessive file downloads or frequent USB usage.
Behavioral analytics tools can track and analyze these patterns. Use these tools to monitor shifts in how employees interact with your systems and data. Communicating with other departments like HR to correlate digital indicators with observable behavior changes is important, ensuring a holistic approach to identifying potential threats.